- What is Directory Service?
- Active Directory
- History of Directory Service
- Advantage of LDAP
- Back to Active Directory
- Naming conventions
- Requirement of DNS
- AD objects
- AD Database
- Schema
- Domain, Tree, and Forest
What's a directory service?
- A directory service is a container that provides a hierarchical structure and allows to store objects for quick and easy access and manipulation. A directory service is like an electronic phone directory that lets you search for Name and retrieve the phone number, address, or other information without knowing where that person lives.
- Before directory services, If you needed a file, you needed to know the name of the file, the name of the server on which it is stored and its folder path. Now this works well on a small network, but as the network grows it becomes challenging.
- Directory service is the means by which users and administrators can locate resources regardless of where those resources are located.
- Also the earlier typical user could have more than one user account or password, and as the network grows and the number of username and password also increases, like one for File Server, one for an email server, etc.
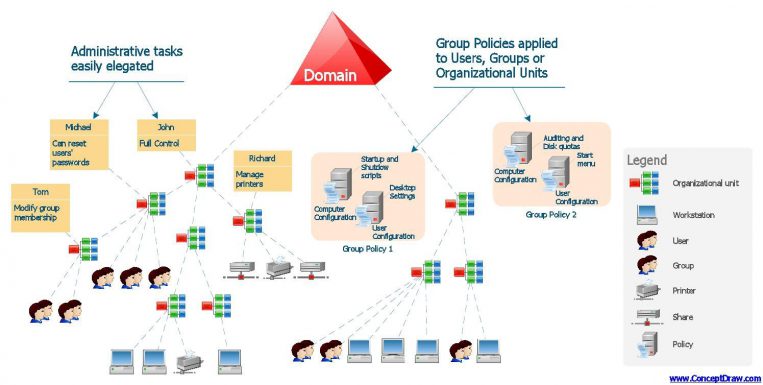
Active Directory
- Active Directory is Microsoft’s answer to directory services and it does a lot more than just locating resources.
- Active Directory takes care of this by using Kerberos Authentication and Single Sign-On (SSO). SSO means the ability of Kerberos to provide a user with one set of credentials and grant them access across a range of resources and services with that same set of credentials. Kerberos authenticates the credentials and issues the user a ticket with which the user gains access to the resources and services that support Kerberos.
- Active Directory also makes user management easier as it acts as a single repository for all of this user and computer-related information.
History of Directory Service
- Earlier to today’s directory services is X.500 specification that emerged from the International Telecommunications Union (ITU), formerly the CCITT (Comité Consultatif International Téléphonique et Télégraphique).
- X.500 sits at the Application layer in the OSI model. X.500 contains several component databases that work together as a single entity.
- The primary database is the Directory Information Base (DIB), which stores information about the objects. The major limitation was its lack of integration with Internet Protocol (IP).
- The protocol it used was Directory Access Protocol or DAP. DAP offered more functionality than that is required for implementing directory services, so a scaled-down version called Lightweight Directory Access Protocol (LDAP) was made. Later it was considered as a standard by Internet Engineering Task Force (IETF).
Advantage of LDAP
- LDAP relies on the TCP/IP stack rather than the OSI stack
- Integrate with IP and enable IP clients to use LDAP to query directory services.
- LDAP can perform hyper-searches. Giving one directory the ability to defer to another to provide requested data.
- LDAP’s API is C-based
- Like X.500, LDAP uses an inverted-tree hierarchical structure
- LDAP supports Kerberos authentication, Simple Authentication Security Layer (SASL), and Secure Sockets Layer (SSL)
- Simple Authentication and Security Layer (SASL) is a framework for authentication and data security in Internet protocols.
Back to Active Directory
- AD is Microsoft’s answer to directory services and it does a lot more than just locating resources.
- AD uses LDAP as its access protocol.
- AD relies on DNS as its locator service, enabling clients to locate domain controllers through DNS queries.
- Lets Understand Active Directory in more detail.
Naming Conventions
- AD contains information about objects in your enterprise.
- These objects can be computers, users, printers etc.
- AD is a container with nested containers holding other containers or objects.
- And we name these containers and objects so that its easy to query or search.
AD supports several Naming Conventions.
- User Principal Names, or UPN
- LDAP names are also known as Distinguished Name
User Principal Names, or UPN
- This one you’ll probably find most familiar is as per RFC 822 specification.
- This has the same format as your email address: Like ashwin@road2master.ms
- They take the form user@domain
- If you have a user named User01 under Active Directory domain Domain01.local, the UPN will be User01@Domain01.Local
- We will discuss more AD domains later.
- In AD you can create custom UPNs too, which means you can also add User01@Domain01.com or User01@xyz.com as UPN for the above-mentioned object.
- More on these later.
LDAP names also known as Distinguished Name
- Typically it has this format
cn=common name
ou=organizational unit
dc=domain
for eg. cn=Ashwin,ou=Trainer,dc=Road2Master,dc=ms
- And query should look like this for the
LDAP://R2MAD01.road2master.ms/cn=Ashwin,ou=Trainer,dc=Road2Master,dc=ms
R2MAD01.road2master.ms is the FQDN of the Domain Controller.
Requirement of DNS
- DNS Server must support
- Service resource (SRV) records
- Dynamic update protocol specified by RFC 2136
- AD relies on DNS as its primary locator service, although its not the only mechanism for locating domain controllers (DCs).
- Domain Controller is the server that has Active Directory Installed.
- When a Domain Controller starts,
- It registers both its DNS name and NetBIOS name. More on NetBIOS name later.
- It add LDAP-specific SRV records in DNS to enable LDAP clients to locate DCs through LDAP queries.
- It also add Kerberos authentication protocol-specific SRV records to enable clients to locate servers running the Kerberos Key Distribution Center (KDC) service.
- Also each DC also adds an A record that enables clients that don’t support SRV records to locate the DC through a simple host record lookup. You can disable this if required.
Active Directory objects
- Objects in AD can be either container for other objects or they can be leaf objects, which do not serve as containers.
- Objects in AD have attributes, and these attributes not only define the object but also store data. This defines the character of that Object.
- Some attributes and optional and some are mandatory.
- Optional: Phone Number
- Mandatory: Username
- When an Object is created AD assigns a GUID, which is a 128-bit number and no two objects in AD have the same GUID.
- And If an object is moved from AD, it doesn’t delete its GUID.
- Objects in AD are protected by Access Control Lists (ACLs).
- More on Security later.
Active Directory Database
- The ESE comprises of tables that define the structure of the directory.
- The Database Layer has three partition that define the contents of AD with an optional 4th table or partition.
Schema Partition
- This stores Active Directory Schema.
- Active Directory Schema defines what are the types of objects that can be created in the directory
- How are those objects relate to one another, and what are the mandatory and optional attributes of each object.
- And how can one create such objects?
Configuration Partition
- This contains the configuration of AD.
Domain Partition
- This partition stores the objects.
Application Partition
- This is an optional 4th partition that an administrator can create.
- More about Active Database in the upcoming parts.
Active Directory Schema
- Active Directory Schema defines what are the types of objects that can be created in the directory
- How are those objects relate to one another, and what are the mandatory and optional attributes of each object.
- And how can one create such objects?
- Schema requires updates whenever you need to create a new type of object or add anything that requires new attributes.
Domain, Tree and Forest
AD Domain
- Objects that are made on AD are grouped into domains.
- The objects for a single domain are stored in a single database (which can be replicated).
AD Domain Tree
- A tree is a collection of one or more domains
AD Forest
- A forest is a collection of trees that share a common global catalog, directory schema, logical structure, and directory configuration.